The following steps describe how to configure SAML SSO in Active Directory Federation Service (AD FS).
Download the SSO settings for your iManage environment
Before you begin, download your iManage environment settings in XML format. These settings are used to configure Microsoft Active Directory Federation Service (AD FS) using information about your iManage environment.
In iManage Control Center, browse to Network & Security > Single Sign-On (SSO).
Select Download XML in the SAML Service Provider Settings section. Save the file for use in Configure SSO in Microsoft AD FS.
Configure SSO in Microsoft AD FS
Complete the following steps in Microsoft AD FS to configure single sign-on for iManage users.
For more information, visit Create a Relying Party Trust.
NOTE: The instructions may vary based on your version of Microsoft Windows Server.
In Server Manager, select Tools, and then select AD FS Management.
Under Actions, select Add Relying Party Trust.
NOTE: If switching from OpenID Connect (OIDC) SSO to SAML SSO in iManage Control Center, we recommend that you create a new Relying Party Trust. Creating a new Relying Party Trust allows you to preserve your existing SSO Relying Party Trust and roll back to it if necessary.Complete the steps in the To create a claims aware Relying Party Trust manually section using the following selections:
On the Welcome page, select Claims aware and select Start.
On the Select Data Source page, select Import Data about the relying party from a file.
Select Browse, then locate and select the XML file you downloaded from iManage Control Center in Download the SSO settings for your iManage environment.
Select Next.
On the Specify Display Name page, enter a descriptive name in the Display name field—for example, iManage—and then select Next.
On the Choose Access Control Policy page, select the access control policy required for your configuration, such as Permit Everyone, and then select Next.
On the Ready to Add Trust page, review your relying trust configuration settings, and then select Next.
On the Finish page, select Configure claims issuance policy for this application, and then select Close.
The Edit Claim Issuance Policy for <server> window opens.On the Edit Claims Issuance Policy for iManage page, select Add Rule.
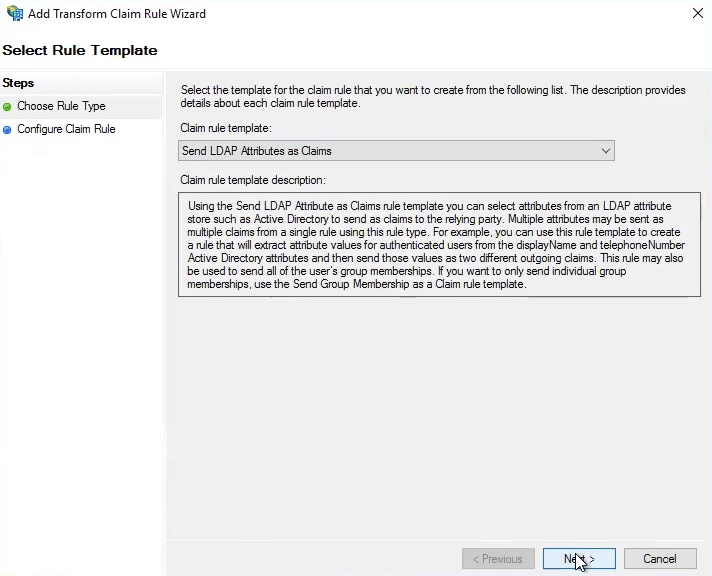
Choose Send LDAP attributes as claims, and select Next. The Add Transform Claim Rule Wizard is displayed.
Figure: Add Transform Claim Rule WizardIn the Add Transform Claim Rule Wizard, select Next.
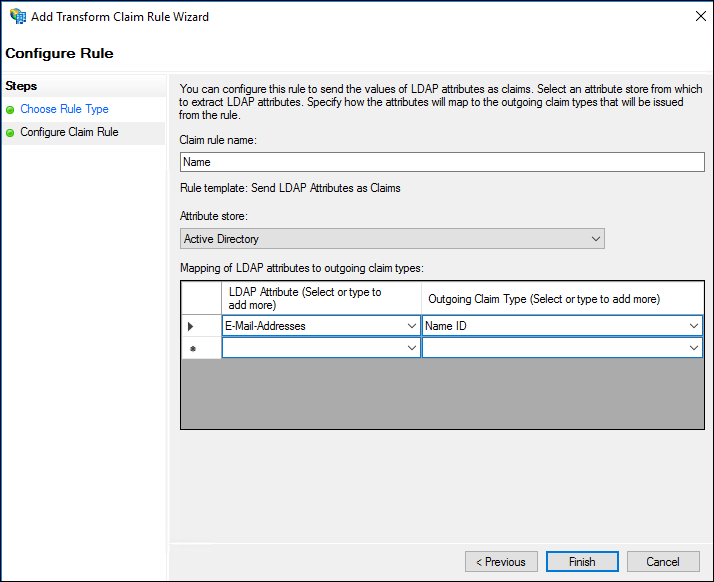
In the Configure Claim Rule step, enter or select the following information:
In Claim rule name, enter Name.
In Attribute Store, select Active Directory.
In the Mapping section, select:
LDAP Attribute: E-Mail-Addresses
This value must match the format of your iManage user IDs in iManage Control Center.Outgoing Claim Type: Name ID
Figure: Configure Claim Rule
Select Finish.
Select Save and then select Apply.
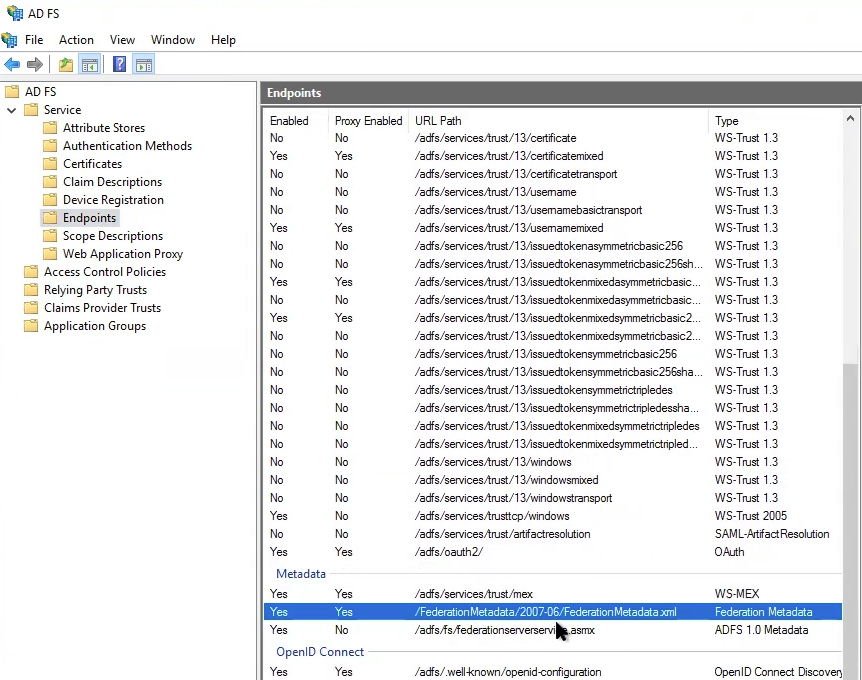
Browse to AD FS > Service > Endpoints.
Locate and select the entry for the Federation metadata.
Figure: Federation MetadataIn a browser, enter the URL for your Windows Server followed by the path shown for the federation metadata—for example:
https://<server_name>/federationmetadata/2007-06/FederationMetadata.xml
The XML file is displayed in your browser.To save the displayed XML as a file, right-click in your browser, and select Save As.
Enter a file name and select Save.
Import the Federation Metadata XML file into iManage Control Center by returning to iManage Control Center and completing the steps in Enable SAML SSO.
NOTE: Any users who were actively signed in to iManage Work when this configuration change occurs will receive an error message "SAML Login Error - logout_not_success" if they attempt to sign out. This is expected behavior for this one-time only. After launching a new browser, signing in or out of iManage won't trigger this error message.
Configure AD FS to sign the SAML response and assertion
To configure AD FS to sign both the SAML response and assertion:
Open Powershell.
Run the following command, and replace <relying party display name> with the display name you configured in Step 3.e in Configure SSO in Microsoft AD FS.
Set-ADFSRelyingPartyTrust -TargetName <relying party display name> -SamlResponseSignature “MessageAndAssertion”
For example:Set-ADFSRelyingPartyTrust -TargetName iManage -SamlResponseSignature “MessageAndAssertion”
Run the following command, and replace <relying party display name> with the display name you configured in Step 3.e in Configure SSO in Microsoft AD FS.
Set-ADFSRelyingPartyTrust -TargetName <relying party display name> -SigningCertificateRevocationCheck None
For example:
Set-ADFSRelyingPartyTrust -TargetName iManage -SigningCertificateRevocationCheck None
Troubleshooting
If users receive error "Authentication Failed. Code: 400-authFailed" when attempting to sign in to iManage Work, the most likely reasons are:
The expiration of the SAML certificate. To resolve the issue, follow the steps in Update your IdP certificate to generate a new certificate and update the certificate in iManage Control Center.
The user doesn't exist in the library. For more information about user library management, refer to Users.
You can also review the AD FS logs for errors if single sign-on isn't performing as expected:
Open Event Viewer and browse to Applications and Services Logs > AD FS > Admin.
If further assistance is needed, contact iManage Cloud Support.