NOTE: To perform operations on the Library Encryption page:
To view the Library Encryption page, or add or manage primary keys, the user signed in to iManage Control Center must be assigned to a Global Management role which has the Key Management privilege. For more information, see Global privilege descriptions.
To apply keys to an iManage Work library, the user must also be a member of the NRTADMIN group in that library.
NOTE: The Encryption Keys option available previously in the iManage Control Center navigation panel has been renamed to Library Encryption.
Introduction
Data encryption is a security measure that prevents visibility of documents in the case of unauthorized access or theft. Also called data at rest encryption, the data files are encrypted when they aren't being used. This encryption is compliant to HIPAA and other American statutes protecting sensitive information from accidental or wrongful disclosure. In the event they're compromised, such as by theft or unauthorized access (including internal unauthorized access), the files are encrypted, and therefore unreadable. When an authorized user accesses a document (such as through editing or viewing within a client application), the document is decrypted and can be read or edited by the user. When the user finishes editing a document, it's returned to its encrypted state.
Encryption of files in iManage Work in the Cloud is automatic and can't be disabled.
Encryption Overview
Encryption uses an electronic cipher, called an encryption key. Encryption keys are implemented in one of two ways: A system-managed key (refer to System managed encryption key), or optionally, Customer Managed Encryption Keys generated in Microsoft Azure (refer to CMEK).
System managed encryption key
iManage Work in the Cloud encrypts all documents using encryption keys managed by iManage. With this model, iManage manages the encryption keys, and you do not have the ability to see details about the encryption or keys.
CMEK
TIP:
For a quick introduction to CMEK, we recommend watching A practical guide to implementing Customer Managed Encryption Keys (login required).
CMEK enables customers to manage their own encryption keys. Customers control their entire process from generating the customer supplied encryption key (the source key), to loading the keys into iManage Work, deciding when to use each key, and when to revoke or replace keys. For improved security, this process uses a dual-party CMEK where two separate key stores are required. The dual-party CMEK process requires two customer team members, known as key holders, with each independently storing a copy of the same primary key in a Microsoft Azure key vault account. The two key stores are then validated by iManage so that:
iManage Work has access to each of the copies of the key inside two separate Azure key vaults, and
The keys in both Azure key vaults are identical to each other.
Once validated, that key can be applied to an iManage Work library for encryption. However, if both keys are revoked, encryption and decryption will be stopped. In this scenario, documents will no longer be accessible, and documents can't be downloaded or uploaded.
Implementing dual-party CMEK in iManage Work follows this process with the customer completing each step:
Create the customer supplied encryption key. This is the source encryption key that'll be the basis for the rest of the process. Refer to Creating the customer supplied encryption key.
A copy of the customer supplied encryption key should be stored by the company in escrow.
IMPORTANT: If this key is lost, or the password is lost, all documents encrypted from this key will be unrecoverable.The customer supplied encryption key is copied twice. Two people, known as key holders, each receive one copy.
Each key holder creates a separate Azure key vault and imports the copy of their customer supplied encryption key. This is known as the key store.
Each key holder provides their Azure key vault domain name system (DNS) name to iManage.This allows the customer to pre-authorize the vaults that are permitted for use. Refer to Registering the Azure key vault domain names with iManage.
Each key holder then provides their key store values to an authorized iManage Control Center system administrator. This administrator must be an NRTADMIN and also have the global Key Management privilege. The iManage Control Center system administrator will create a primary key based on the two key stores. Refer to Adding a primary key.
The customer applies this primary key in iManage Control Center to selected libraries. Refer to Applying a key to an iManage Work library. Immediately after applying the key, the library uses this primary key for all document encryption and decryption of new documents added to the library. In addition, a key rotation process is automatically initiated to substitute the keys for protecting the library's content. For more information, refer to Understanding key rotation and tracking key rotation progress.
If you implement CMEK in iManage Control Center, you can revert to the default encryption system at any time.
On this page:
Creating the customer supplied encryption key
Use this to create the customer supplied encryption key.
The process to create customer-supplied encryption keys and key vaults is completed outside of iManage Work. As part of the best practices and understanding important aspects of the process, iManage recommends certain guidelines. See Azure Key Vault for more information.
Use the Azure Information Worksheet to identify and record the key and key vault information for later use in these processes.
Registering the Azure key vault domain names with iManage
Before managing encryption keys within iManage Control Center, the customer's Azure key vault domain names must be registered with the iManage Work system.
To register your Azure key vault domain names with iManage, open a support request with iManage Cloud Support providing the two Azure key vault domain names, also called a DNS name. Use the value recorded on line 1 of the Azure Information Worksheet. These two domain names must be different. For example, key holder 1 might be
azurevault1.vault.azure.net, and key holder 2 might beazurevault2.vault.azure.net.The key holders receive verification from iManage Support that the key vault DNS names have been successfully registered with the iManage Work system before continuing.
Adding a primary key
A primary key must be added before applying it to one or more iManage Work libraries.
Within iManage Control Center, browse to the Library Encryption page (Network & Security > Library Encryption):
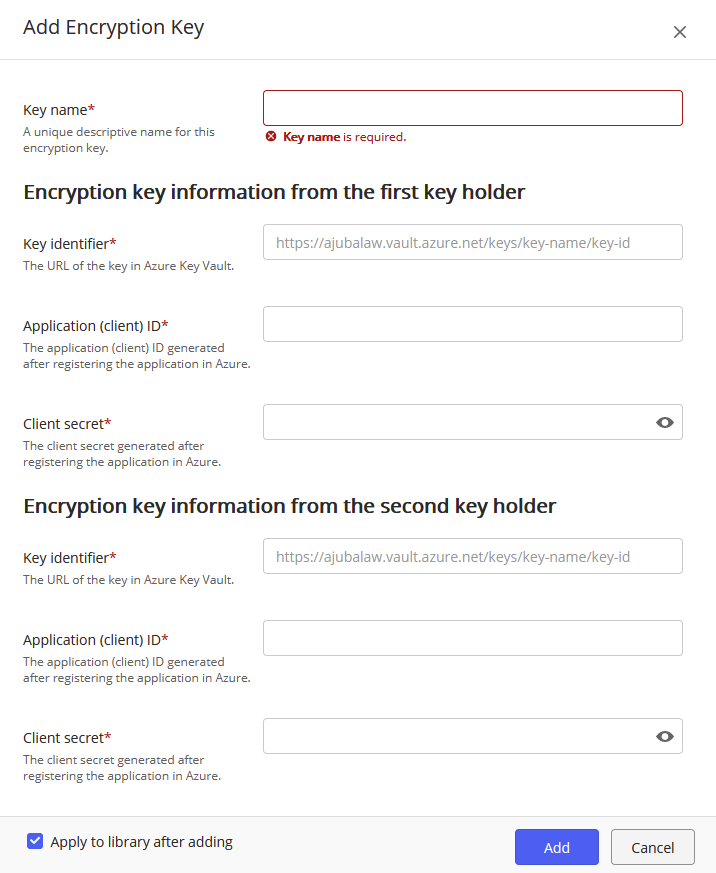
Select Add encryption key. The Add Encryption Key dialog is displayed.
Figure: Add Encryption Key dialogEnter the Key name. This is a descriptive name intended to conveniently identify the key. This name is displayed in the key list. It cannot be the same as any other existing key but can be changed later.
In the Encryption key information from the first key holder section, enter the following information from the first key holder:
Key identifier: (also called the Azure Key Version Key Identifier) The combination of the URI and key identifier from the process used to create the Azure key vault. Use the value recorded on line 2 of the Azure Information Worksheet for the Azure Key Version Key Identifier. For example:
https://azurevault1.vault.azure.net/keys/ajubalaw-2/7668e37b63f6433fa285434f23a58b1bApplication (client) ID: A string identifier provided during the application registration in the Azure Active Directory. Use the value recorded on line 3 of the Azure Information Worksheet for the Application ID. For example:
https://azurevault1.vault.azure.net/keys/ajubalaw-2/7668e37b63f6433fa285434f23a58b1bClient secret: A client secret provided during the application registration in the Azure Active Directory. Use the value recorded on line 4 of the Azure Information Worksheet for the Client secret. For example:
xCGRvvvQmKfqwTw[@a@qovRN_Nn72K46
All of these values must be different than the second key holder's values.In the Encryption key information from the second key holder section, enter the equivalent information from the second key holder. All of these values must be different than the first key holders values.
(Optional) To also apply this new primary key to one or more iManage Work libraries, select the Apply to library after adding option.
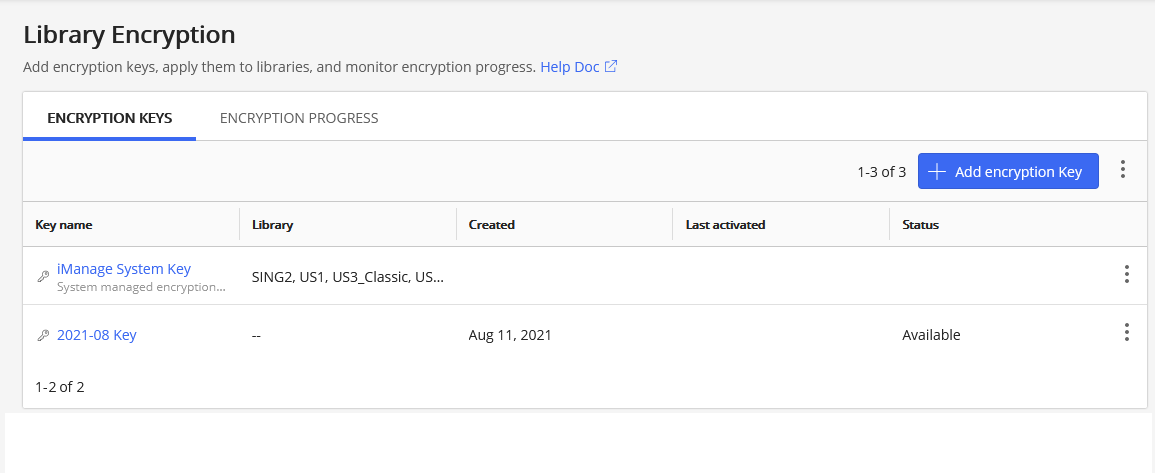
This will automatically open the Apply key to library dialog. For more information, refer to Applying a key to an iManage Work library.Select Add. The newly added key is displayed with the status of Available.
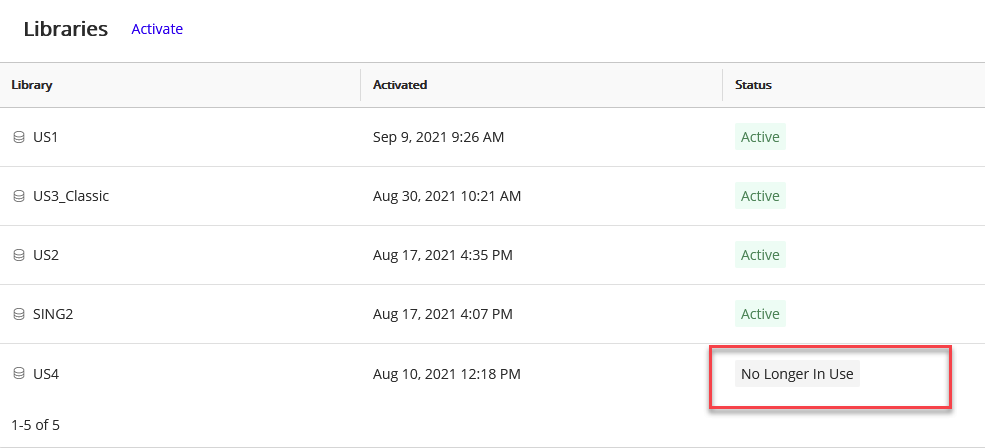
Figure: Library Encryption
Applying a key to an iManage Work library
A primary key is activated by applying it to one or more iManage Work libraries. Primary keys can be applied to libraries as needed. The previous primary key is deactivated. As a best security practice, we recommend not reusing previously used primary keys. The exception is the built-in iManage system key which can be reapplied at any time.
Within iManage Control Center, browse to the Library Encryption page (Network & Security > Library Encryption):
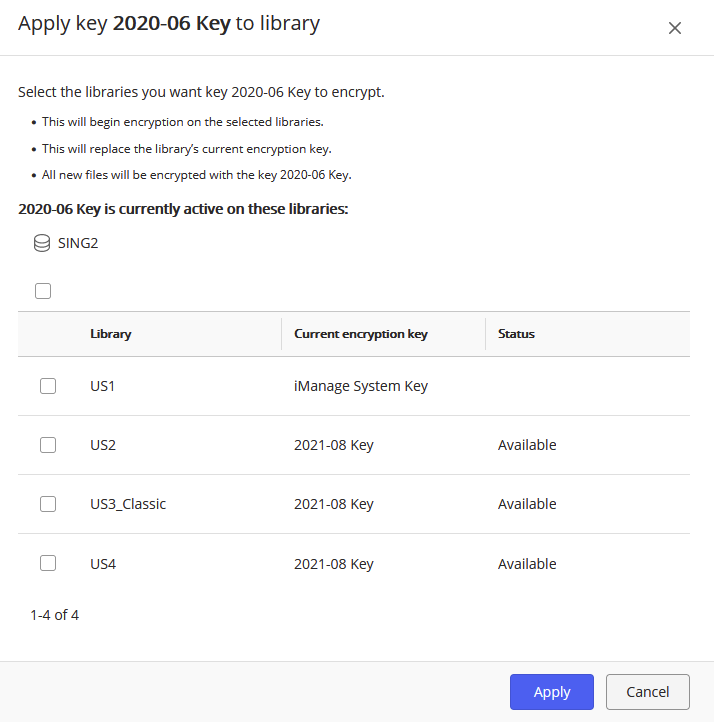
Right-click a primary key, and select Apply to library. Only apply a key with a status of Available in Control Center. For more information about the status of keys, refer to Understanding encryption key status.
Figure: Apply key to library dialogSelect one or more libraries that you'd like this primary key to apply to.
Select Apply. The Encryption Keys page displays.
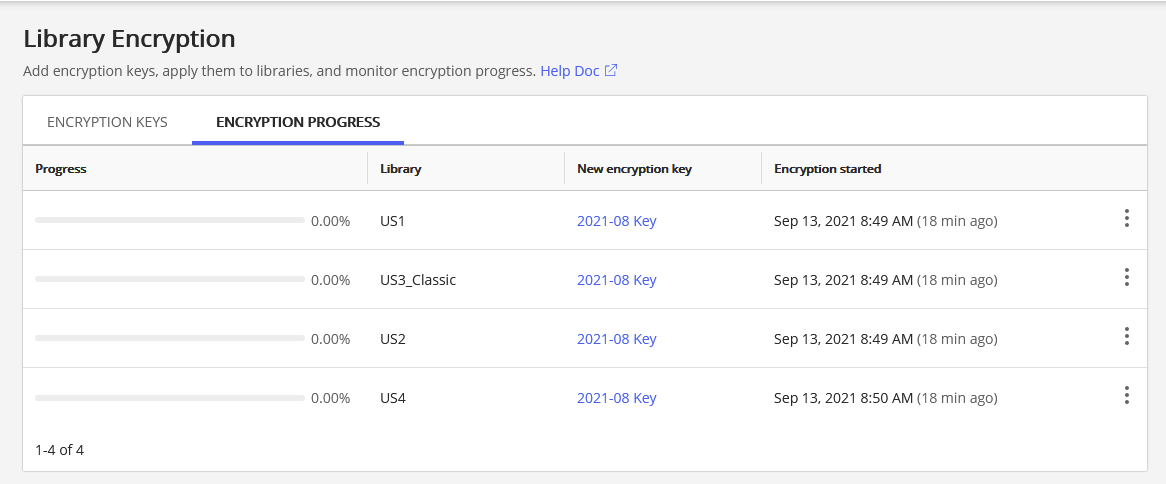
To see the progress of the encryption process, select the Encryption Progress tab. For more information, refer to Understanding key rotation and tracking key rotation progress.
This newly applied primary key will be used in all the encryption going forward. While a primary key is applied to a library, it's called a library key. Documents are encrypted and decrypted with the library key.
A library key can't be deselected or deactivated. It becomes deselected or deactivated only when a new primary key is applied to that library, in essence replacing the library key.
Understanding key rotation and tracking key rotation progress
When a new key is added to iManage Control Center and then applied to an iManage Work library, a process of substituting the keys that protect the content within the library is initiated. This process is also called a key rotation.
The status of the key rotation is displayed on the Encryption Progress tab and in the Key Details page in iManage Control Center.
NOTE: After a key is applied to a library, the encryption progress is updated approximately every hour.
When the process is complete, the entry is removed from the Encryption Progress tab.
Understanding encryption key status
The status of primary keys is shown on the Library Encryption key page.
Available: The key has been successfully added to the system, and both key stores are in a healthy state (not revoked).
Key Store 1 Revoked | Key Store 2 Revoked | Both Key Stores Revoked: One or both of the key stores have been revoked for this key.
NOTE: For the iManage System Key, no status is shown.
The status of the key as applied to individual libraries is shown on the encryption key Details page.
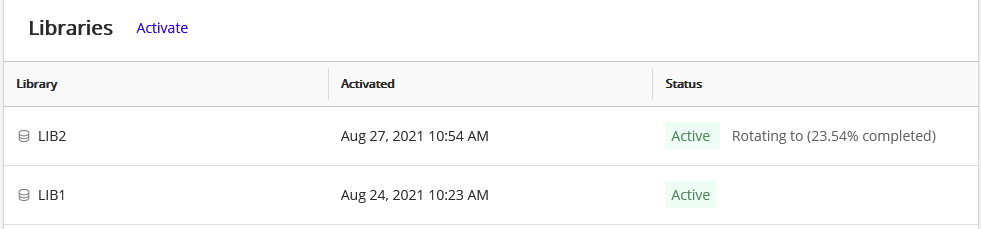
Active: This key is actively being used to encrypt the contents of this iManage Work library.
If a key rotation is in process, the status also displays the percentage complete, for example: Active: Rotating to (76.54%).Inactive: Rotating from: A key rotation (rekeying) process is actively moving from this key to the new key. New content added to this library won't be encrypted using this key.
No longer in use: All content previously using this library key has been re-keyed using a new primary key.
Updating the Azure Key Store client id or secret
Microsoft Azure generates a secret for Enterprise Applications to grant access to each Key Store in your Azure Key Vault. Microsoft Azure enforces an expiration date on the client secret (maximum 2 years) for each Key Store within Azure Key Vault. If this secret expires, Azure blocks access to the keys stored in the Key Vault. If this occurs, iManage Cloud cannot access the Key Vault, your existing content cannot be decrypted, and new content will not be able to be uploaded or encrypted.
NOTE: Please be aware of the expiration of your Key Store client secrets. It is your responsibility to track these expiration dates and generate new secrets accordingly.
Before this expiration date, you must:
Generate a new secret for each Key Store in your Azure Key Vault.
Update the secret in iManage Control Center.
IMPORTANT: After updating the credentials to the key stores (application ID or secret) in iManage Control Center, ensure the key holders don't remove the old secrets (and optionally application IDs) from their respective Azure accounts for at least 24 hours.
This time is required for iManage Work to propagate the new credentials across all data centers and regions, and to ensure that all cached credentials are refreshed with the new credentials.
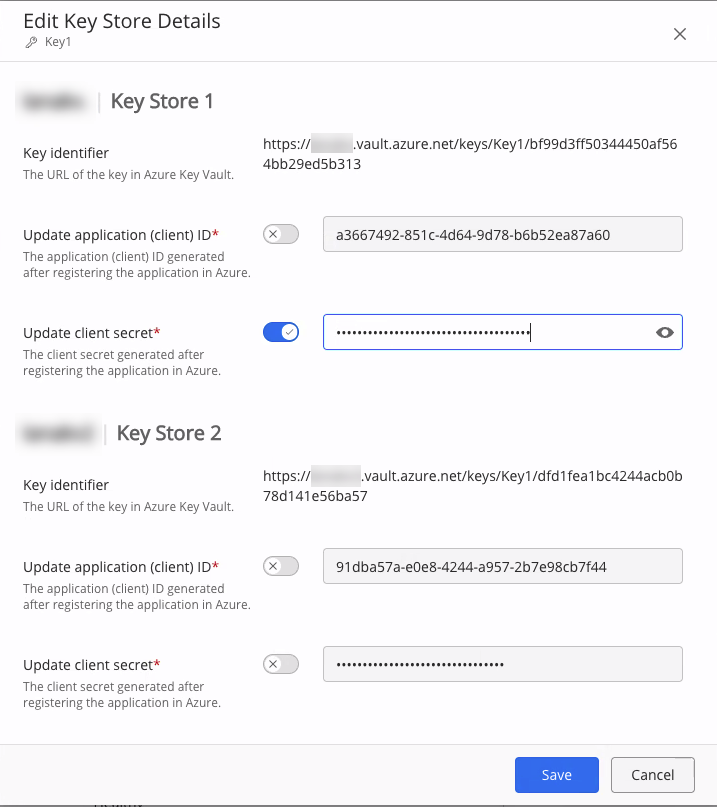
To update the Azure Key Store credentials, such as the application (client) id or client secret:
Within iManage Control Center, browse to the Library Encryption page (Network & Security > Library Encryption).
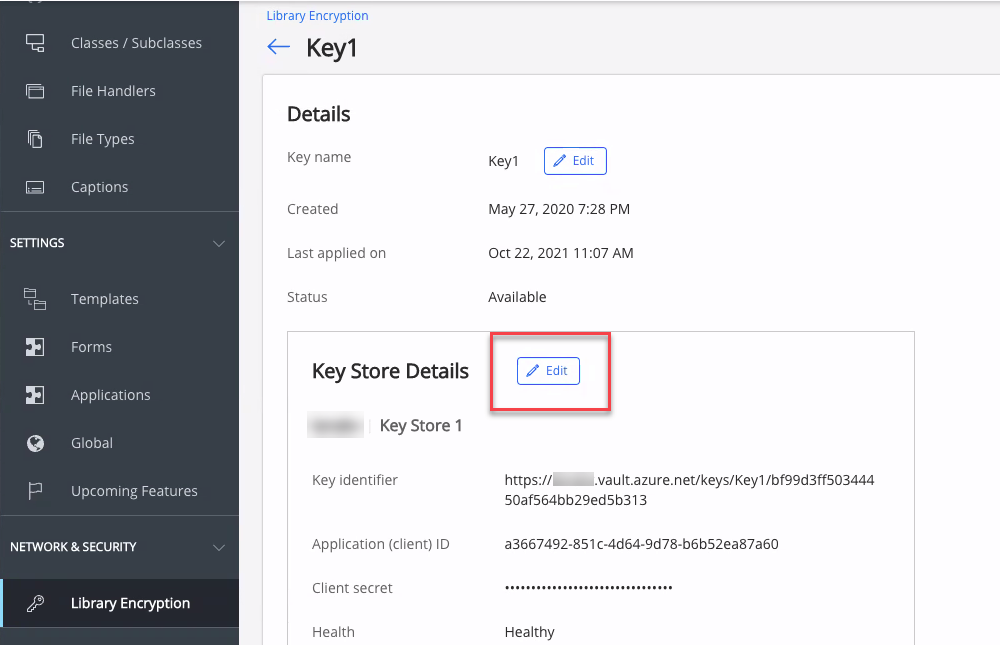
Select the key name to open the key details page.
In the Key Store Details section for this key, select Edit.
Figure: Key Store DetailsThe Edit Key Store Details dialog is displayed.
Figure: Edit Key Store DetailsSelect the toggle switch beside the field you want to update, then enter the new value.
The Key Identifier can't be changed.
If you update an application (client) ID, you must also enter the new client secret associated with this application ID.Select Save.
Editing the key name
Use this to edit a primary key name. Editing the key name doesn't change the status of the primary key.
Within iManage Control Center, browse to the Library Encryption page (Network & Security > Library Encryption).
Right-click the key name to be edited.
Select Edit key name. The Edit dialog displays.
Enter the new primary key name. The name can't be the same as another primary key name.
Select Save.
Viewing key details
The key detail page provides information about the key and the libraries to which it's been applied.
Within iManage Control Center, browse to the Library Encryption page (Network & Security > Library Encryption), and select an encryption key from the list. The details screen displays.
FAQ
General
Q: Is my data encrypted if I don’t use CMEK?
A: Yes, data is encrypted using the same mechanism as CMEK with a key owned and managed by iManage.
Q: How do I check that CMEK is enabled?
A: Sign in to iManage Control Center as a user with the Key Management privilege enabled for their role. Browse to Library Encryption, then select the key intended for encryption. Each library will have an individual status. Enabled signifies the key is enabled for that particular library. The iManage System Key is enabled on all libraries by default.
Q: Should I enable CMEK?
A: The decision to use CMEK is unique to each customer, and is made solely by the customer. You can switch to the customer managed keys, and revert to iManage system keys at any time. Customer Managed Keys can be applied at any point before or after go-live. Once a customer managed key has been activated on a library, a key rotation process is automatically initiated to protect the library’s content using the new key. The key rotation timeline varies depending on the size of the library. As a guideline, you can expect the rotation to progress at a rate of approximately seven million document versions per day. For other common questions regarding key rotation, refer to Understanding key rotation and tracking key rotation progress.
Q: Can the same key be applied to multiple libraries?
A: Yes, separate keys aren't required for separate iManage Work libraries.
Q: Can our firm use the same key between our production and our sandbox environments?
A: It's important to understand that the same key vault and key id can't be used more than once. Each time a key is uploaded to a key vault a new key id is issued. There's no restriction on the number of times that an RSA key can be used. The CMEK service performs the following checks:
The same key vault isn't utilized by multiple environments
A copy of the same key is used in both vaults
The same key id isn't used.
Q: Can I delete or archive encryption keys that are no longer being used?
A: Currently, this isn't possible. However, there's a request for this functionality in the iManage Idea Bank: Add ability to archive CMEK in Control Center (login required).
For more information, refer to Customer Guide to the iManage Ideas Bank (login required).
Q: Can I modify the Azure credentials (application id & client secret), without needing to perform a full rotation?
A: Yes, this is available. Instructions can be found in Updating the Azure Key Store client id or secret.
Q: Does my encryption key ever leave my vault or cross regional boundaries?
A: No. The key is called by the iManage service within the library region to wrap or unwrap content, but it isn't accessed or directly handled by any iManage services, and it doesn't leave the region.
Key rotation
Q: How long does the key rotation process take?
A: The system must update encryption for all documents within the library. The time required to complete this activity varies based on system utilization and the number of documents in the library. When a key is applied to multiple libraries, the key rotation process occurs concurrently on each library.
Q: While a key rotation is in progress and a user adds a new document to the iManage Work library, is it encrypted with the old key or the new key?
A: As soon as a new key is applied to a library, all new documents and emails added to the iManage Work library are encrypted using the new key. The Encryption Progress tab in Control Center shows the key rotation progress for existing documents in the library.
Q: What happens if I have applied a new key (key 1 is replaced by key 2) and that rotation is still in progress, and I then I apply another new key (key 3) on the library?
A: The existing key rotation to key 2 is stopped at its current point, and a new rotation is started using key 3. Documents protected with key 1 and key 2 will be transitioned to use key 3.
Q: After applying a new key to a library, when is it safe to revoke this key in Azure?
A: When a new primary key is applied to a library and the key rotation has completed, the Key details page shows the key with a status of No longer in use.
IMPORTANT: Never revoke a key in Azure until you first confirm the No longer in use status for all libraries for which the old key was applied.
Additionally, we recommend waiting for 90 days after the key is listed as No longer in use in the event that iManage needs to restore any content from a backup.
Terms
The following terms are used during for encryption key process.
Term | Meaning |
|---|---|
Created (date) | The date when a primary key becomes the actively used key for encrypting data. Refer to Adding a primary key. |
Last applied on (date) | The most recent date when the primary key entry was applied to any library. Refer to Applying a key to an iManage Work library. |
Application (client) ID Client secret | The first of two string identifiers provided during application registration in the Azure Active Directory. The other identifier is the Client secret, similar to a password, provided during the application registration in the Azure Active Directory. Each key holder will have a different Application (client) ID and secret. |
Customer-managed encryption key (CMEK) | The general term for the process in which the customer supplies and manages their own encryption keys. Customers control their entire process, from generating the customer supplied encryption key (the source key), to loading the keys into iManage Work, deciding when to use each key, and when to revoke or replace keys. The iManage Work version implements a dual-party process that requires validation of two independent key stores. |
Customer supplied encryption key | The source encryption cipher that'll be the basis for the primary key used to apply encryption for libraries. The customer creates their own source encryption key and independently copies it to two team members, called key holders. |
Global key management privilege | The global Key Management privilege. With the privilege enabled, users can view the Library Encryption page in iManage Control Center, and add and manage primary keys. Users must also be a member of the NRTADMIN group of an iManage Work library to apply the key to the library. For more information, refer to Global role setting of Key Management. |
iManage | The customer's designated customer success manager (CSM) or their implementation partner. This is an iManage-designated system administrator who must register each of the key holders' key store information. |
iManage system key | The encryption key(s) provided by and managed by the iManage Work system. This is a default primary encryption key. Use this key if you choose not to manage your own encryption keys. |
Key address | The URI of a key holder's Azure key vault that contains the primary key. Each key holder will have a different address. |
Key health | The status showing a key's ability to be accessed: Available: The key can be accessed and has the ability to be actively used for encryption/decryption. Unavailable: The key can't be accessed and its ability to be actively used can't be assessed. It hasn't been revoked but only the access to it is being hindered, such as from a network outage. Revoked: The key has been temporarily disabled by the customer. A single unrevoked key is still able to encrypt or decrypt documents. If the revocation isn't intended, the cause should be quickly evaluated. Two revoked keys won't be able to encrypt or decrypt documents. Intentionally revoking both keys represents an extreme case, likely due to a catastrophic security event. Keys can be unrevoked at any time by the customer. IMPORTANT: If both keys are revoked, new documents can't be uploaded to iManage Work, nor can documents be viewed or downloaded. |
Key holder | A key holder is a customer user who created a separate Azure key vault that contains a copy of the customer supplied encryption key. There'll be two key holders, known as key holder 1 and the key holder 2. |
Primary key name | The name of the primary key entry in iManage Control Center used to easily identify the primary key. The name may be changed later. The name can't be the same as another primary key name. |
Key version | This is a 32-character string identifier provided during the Azure key generation process. Each key holder will have a different key version. |
Libraries | One or more target libraries that the encryption affects. A library itself isn't encrypted, only the documents within a library are. |
Primary key | The key that is applied to libraries that allows the encryption and decryption of documents. Primary keys appear on the Library Encryption page in iManage Control Center. It's created by the customer from the two key holders who independently stored a copy of the same customer supplied encryption key in secure Microsoft Azure vaults. Links to those vaults are provided to their iManage Work system administrator. After iManage Work validates the two Azure vaults, the primary key is generated. |
NRTADMIN | An iManage Work user with NRTADMIN system administration privileges. This user is a member of the NRTADMIN group for the specified library. It's possible that a user can be an NRTADMIN for some libraries but not others. Therefore, care must be taken when an NRTADMIN is attempting to apply an encryption key to a library. |